The clock is ticking on Q-Day, the looming but unknown date when quantum computing could have the capability to rapidly and simply break the encryption keys that preserve most web communication secure.
Experts have recognized concerning the hypothetical risk of Q-Day because the Nineteen Nineties. But Google lately warned that quantum computer systems might have the ability to hack some encrypted methods by 2029 — a timeline that drastically narrows the window to safeguard knowledge that many cybersecurity specialists had beforehand predicted. The new estimate signifies that governments, firms and different entities might have far much less time to put together.
“It’s the day when people, perhaps adversaries, will have access to a quantum computer that can break cryptographic codes that are in use,” stated Michele Mosca, cofounder and CEO of cybersecurity firm evolutionQ.
Q-Day marks the second a quantum pc good points sufficient assets and stability to crack standard crytopgraphy. When that occurs, each monetary transaction, medical file, e mail, location historical past and crypto pockets protected by as we speak’s generally used algorithms might be unlocked by a machine able to fixing the complicated math that presently retains delicate knowledge safe.
At that game-changing turning level, “everything’s safe — safe, safe — and then suddenly it’s not safe. It’s a very drastic jump,” stated Mosca, who can also be a professor on the Institute for Quantum Computing on the University of Waterloo in Ontario.
Adversaries and dangerous actors might already be gathering encrypted knowledge, with the intention of launching “harvest now, decrypt later” assaults. In this state of affairs, info is stolen, saved after which decrypted when a full-scale quantum pc is accessible, he added.
Mosca has coauthored the Quantum Threat Timeline Report, printed by the Global Risk Institute in Toronto, since 2019. The seventh version, printed March 9, recommended a full-scale, cryptographically related quantum pc was “quite possible” throughout the subsequent 10 years, and “likely” within the subsequent 15. Mosca and his coauthor based mostly their prediction on the opinions of 26 specialists.
“Many organizations may be unaware that they are currently exposed to an intolerable level of risk that requires urgent action,” the report authors wrote.
Google stated on March 25 that it was targeting 2029 “to secure the quantum era” with post-quantum cryptography. The timeline mirrored advances within the quantum computing subject, the corporate stated. “By doing this, we hope to provide the clarity and urgency needed to accelerate digital transitions not only for Google, but also across the industry,” it famous in a weblog put up. Similarly, cloud computing providers firm CloudFlare introduced it was also now targeting 2029. Google declined an interview request.
Cryptography is the invisible plumbing that retains the worldwide economic system spinning. Most web safety — consider the tiny padlock image in your web browser — is presently based mostly on encryption that depends on a quirk of math. While multiplying numbers is comparatively simple, the inverse of that course of — factorizing — is just not.
RSA cryptography — named after its creators Ron Rivest, Adi Shamir and Leonard Adleman — is without doubt one of the most typical encryption algorithms and makes use of this method. The Quantum Threat Timeline Report defines a cryptographically related pc as one that might, for instance, break RSA encryption in 24 hours.

Quantum computing isn’t merely a extra highly effective or quicker model of the computer systems in use as we speak. This type of processing works in a basically completely different means.
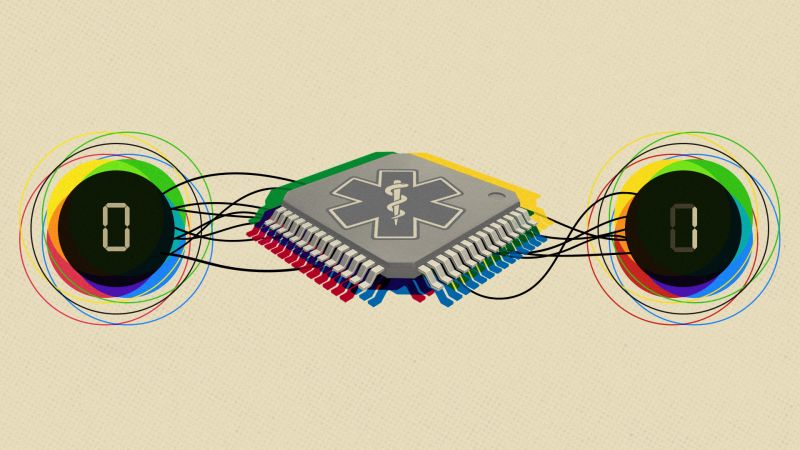
Unlike commonplace computer systems that course of info sequentially utilizing bits (0 or 1), quantum computer systems make use of quantum bits — “qubits” — that may symbolize 0, 1 or each concurrently. Known as superposition, this property allows quantum machines to maintain and course of extra complicated info.
The predominant problem the sector wants to overcome is making extra secure bodily qubits. These delicate parts sometimes solely operate in extraordinarily chilly, high-vacuum environments — circumstances that assist preserve them secure and fewer inclined to errors throughout calculations.

Future quantum computer systems could also be able to breaking the second-generation cryptography that protects cryptocurrency and different methods with far fewer qubits than beforehand realized, in accordance to a March report. The paper was coauthored by Google staff and teachers on the University of California Berkeley, Stanford University, and Ethereum Foundation, a nonprofit that helps the Ethereum blockchain.
Known as elliptic curve cryptography or ECC, the encryption method makes use of extra obscure math than the RSA algorithm; it relies on equations that may be represented as curved traces on a graph, and generates encryption keys based mostly on completely different factors on the road.
Google stated in a March 31 blog post that the analysis workforce discovered an roughly 20-fold discount within the variety of bodily qubits wanted to clear up the elemental math puzzle that underpins ECC. The firm added it developed a new technique to describe the safety vulnerabilities that future quantum computer systems current, “so they can be verified without providing a roadmap for bad actors.”
Most blockchain applied sciences and cryptocurrencies presently depend on elliptical curve cryptography for crucial facets of their safety, the Google put up stated. While viable options exist, the put up added “they will take time to implement, bringing increasing urgency to act.”
The paper has not but been peer-reviewed, however it may be thought of a “warning shot,” significantly to the cryptocurrency group, stated Catherine Mulligan, a visiting tutorial and analysis fellow on the Institute for Security Science and Technology at Imperial College London.
“Cryptocurrencies are inherently incredibly decentralized,” she stated. “The issue is in order to upgrade, you have to get people to agree, and you have to get consensus among the actual engineers to upgrade, and then they tend to argue a lot about how they’re going to do that upgrade,” Mulligan stated.
The excellent news, she defined, is that governments, together with the United States and the United Kingdom, have printed requirements for post-quantum cryptography.
These tips primarily contain software program upgrades that depend on math “orders of magnitude more complex” to clear up than conventional approaches, Mulligan stated. In addition, some firms and governments might pair that with quantum key cryptography, significantly for extremely delicate info.
Quantum key cryptography permits two events aiming to share delicate knowledge to set up a safe encryption key with secrecy ensured by the legal guidelines of physics, not the computational issue of a mathematical downside.
The protocol, first conceived within the Eighties by this yr’s winners of the Turing Prize, entails utilizing photons of sunshine to create a secret key between two events. However, the tactic entails specialist {hardware} that may make it costlier and tough to deploy.
Some researchers examine the quantum risk with Y2K, or the millennium bug, a pc flaw that programmers thought may trigger extreme systemic issues after December 31, 1999.
When the primary pc applications have been being written, engineers used a two-digit code for the yr as a result of in these days knowledge storage was pricey. For instance, for the yr 1977, the date learn 77. As the yr 2000 neared, programmers realized that computer systems won’t interpret 00 as 2000, however as 1900, doubtlessly inflicting disruption.

“I know that we have these doomsday scenarios, where we are sort of scaring everybody,” Mulligan stated. “I’m old enough to remember Y2K. Basically, the reason there was no Y2K is everyone worked hard enough to make sure we didn’t have it.” Mulligan stated she thought that’s what would in all probability occur with the quantum risk to cybersecurity.
However, whether or not the brand new risk might be tackled with related urgency is unclear. Just over 90% of companies nonetheless lack a street map for dealing with quantum safety threats, in accordance to data cited by McKinsey.
The potential prices of not making ready adequately are eye-watering.
A 2023 report by the Hudson Institute, a US conservative assume tank, estimated that a quantum pc cyberattack on the Federal Reserve’s Fedwire Funds Service — its interbank fee system — may set off a monetary collapse and end in a six-month financial recession.
Dustin Moody, a mathematician concerned in post-quantum cryptography on the National Institute of Standards and Technology, a US federal company, stated large, multinational firms have been effectively conscious of the risk and “moving pretty quickly.” However, he stated there was a restrict to the motion people and small firms may take.
“Everyone should be concerned and worried about it,” Moody stated.
“What does the average person need to do? Nothing. I mean, they need to rely on their technology providers and so forth to handle this change for them,” he stated.
“Similarly with smaller mom-and-pop companies, they themselves don’t need to do too much, as long as they just make sure that the products they’re using, they talk to providers and say, ‘There’s this quantum threat, have you taken care of it?’” he added.
The White House recommends 2035 because the yr entities ought to goal to have adopted post-quantum cryptography, Moody stated. NIST finalized a set of encryption algorithms in 2024 designed to stand up to cyberattacks from a quantum pc.
“If everyone were to migrate on time, we’d be in good shape, but the problem is that’s not going to happen in the real world,” he stated. “We’ve had cryptographic migrations in the past, switching from one algorithm to another, typically that takes anywhere from 10 to 20 years, and this migration is going to be more complicated and more costly than the previous ones. So, if a quantum computer comes out in five years, the transition will not be done yet.”
What’s extra, whereas organizations undertake quantum-safe safety, doing so solely will defend future knowledge in opposition to the quantum risk, Moody and Mulligan famous, given the chance that “store now, decrypt later” assaults might already be within the works.
Electronic well being information, which include long-term medical histories and genetic info, might be prime targets for these kinds of assaults. “The thing is, you can upgrade your software, but you can’t really upgrade your DNA,” Mulligan stated.

Seoyoon Jang, a doctoral scholar in electrical engineering and pc science on the Massachusetts Institute of Technology, is working to shield wi-fi biomedical gadgets, comparable to insulin pumps and pacemakers, from potential quantum assaults. These tiny, extensively used gadgets are often too power-constrained to run the computationally demanding safety protocols mandatory in a post-quantum world.
She units out a worst-case state of affairs during which the exterior machine, usually a smartphone that wirelessly connects to the insulin pump to regulate dosage, is hacked. “Imagine, it would be so easy to send a command: ‘Hey release lethal dosage.’ We have to actually care about this,” she stated.” “As we move into remote health monitoring, these devices will be everywhere.”
Together along with her colleagues, Jang has engineered an ultra-efficient microchip, across the measurement of an especially effective needle tip, that features built-in safety wanted for post-quantum cybersecurity. The machine achieved between 20 and 60 instances greater vitality effectivity than different post-quantum safety strategies they in contrast it with. The microchip has a smaller space than many present chips.
The work was partially funded by the Advanced Research Projects Agency for Health or ARPA-H, which Jang stated deliberate to commercialize the know-how. “My chip is as far as I know, it’s the first to actually try to bridge the gap here,” she stated. ARPA-H is a part of the US Department of Health and Human Services.
The newest Quantum Threat Timeline Report stated it’s significantly onerous to consider quantum threat to cybersecurity as a result of “under the radar” analysis efforts — by secret state-backed labs, firms working in stealth or malicious personal actors — may imply that advances in quantum computing are hidden from view.
“Since covert successes would remain invisible for some time, it is safer to assume that the true threat could be closer than what can be inferred from open publications alone,” the report stated.
“The real Q-day may occur before the world becomes aware of it, as states or bad actors potentially seek to use this knowledge to their strategic advantage.”
Sign up for NCS’s Wonder Theory science newsletter. Explore the universe with information on fascinating discoveries, scientific developments and extra.