Two Americans have been sentenced to years in prison for their roles in a covert scheme that defrauded main US firms whereas producing $5 million for the North Korean regime, the Justice Department stated Wednesday.
Zhenxing “Danny” Wang, 39, and Kejia “Tony” Wang, 42, each of New Jersey, had been alleged middlemen in an elaborate conspiracy that concerned tricking Fortune 500 firms to rent abroad tech staff who stole the identities of varied Americans. A federal court docket in Boston sentenced Zhenxing Wang to over seven years in prison and Kejia Wang to 9 years in prison.
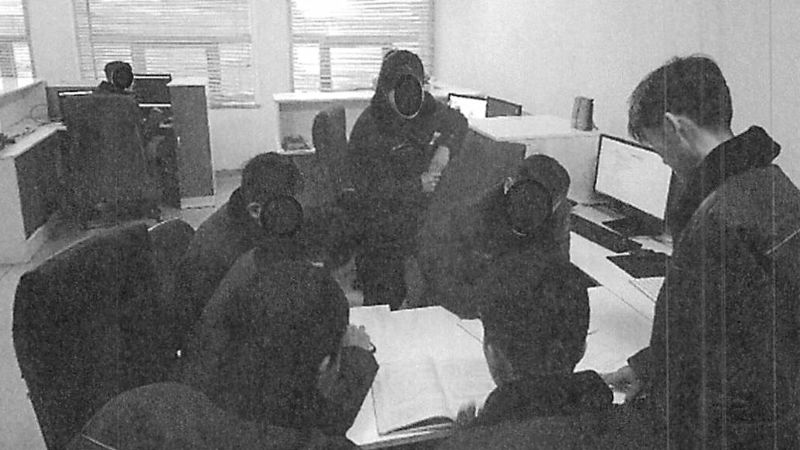
At the guts of the scheme had been “laptop farms” — or clusters of US company-issued computer systems — that Wang and Wang allegedly managed from their properties within the US. Those laptops gave the abroad tech staff a foothold into main American firms to draw salaries and in a single case steal export-controlled knowledge from a California-based protection contractor.
Other firms who unwittingly paid the abroad tech staff embrace a semiconductor distributor in Massachusetts and a software program improvement agency in California, in accordance to prosecutors.
North Korea is more and more turning to such schemes to circumvent sanctions and generate income for its nuclear weapons program, in accordance to US officers. In 2024, prosecutors charged an Arizona girl in an identical scheme that compromised the identities of 60 Americans and affected 300 US firms, together with a “premier” Silicon Valley tech agency.
The North Korean authorities has stolen billions of {dollars} in recent times by hacking cryptocurrency exchanges and utilizing IT staff to infiltrate US tech corporations, in accordance to US officers and personal consultants.
The US authorities has tried to crack down on the schemes whereas publicly and privately warning firms throughout the nation of the evolving menace from North Korean IT staff.
There’s nonetheless loads of work to do: The State Department on Wednesday provided up to $5 million for info on a number of different folks allegedly concerned in producing income for the North Korean regime.
NCS has requested remark from attorneys who represented Wang and Wang. The pair beforehand pleaded responsible to prices associated to the scheme.
The two males allegedly arrange entrance firms in New Jersey to falsely declare that the tech staff had been licensed to work within the US. Other members of the conspiracy allegedly used background-check corporations to determine US individuals whose identities they needed to steal. At least 80 US individuals had their identification stolen, in accordance to prosecutors.
Networks of North Korean tech staff “increasingly rely on U.S.-based LLCs to create the appearance of legitimate employment,” stated Michael Barnhart, a researcher at insider menace agency DTEX Systems.
“Pairing a US person, a US address, and a front company … the facilitators created the illusion of a legitimate domestic ‘effort’ allowing the IT workers to present themselves as U.S.-based without triggering suspicion during onboarding or daily workflows,” Barnhart advised NCS, referring to the scheme related to Wang and Wang.
“A growing number of staffing and recruiting agencies are unknowingly enabling this activity by vouching for these workers, claiming to have completed background checks and due diligence,” Barnhart stated. He additionally warned that North Korean IT staff have embedded themselves at subcontractors “to reach larger targets” that contract with governments around the globe.